How to Break the ROI of SMS Toll Fraud
SMS fraud comes in many forms, all driven by the ubiquity of SMS, the low risk to the attacker, and the instant payoff. Think smishing – a well-known variant where cybercriminals deceive consumers into revealing sensitive information or performing other dangerous activities via text message. Just last week, I received a text from our CEO with a “new number” asking me to reply…these are now almost a weekly event! Then there’s one-time passcode (OTP) interception, a process where bad actors steal passcodes intended to verify online interactions. Layer in reverse proxy phishing, and this attack is sophisticated and serious!
But one of the most pernicious – and escalating – attack vectors is SMS toll fraud.
SMS toll fraud is all about attackers getting in and out quickly, monetizing the flow of high-volume, high-cost SMS messages by ensuring that the charges for these messages are billed to unsuspecting businesses. This type of SMS fraud is growing exponentially as cyberattackers and the colluding carriers have realized it can be an extremely effective way to grab the money and run.
Fortunately, businesses have the means to effectively combat this covert threat. By arming yourself with essential information, implementing best practices, and utilizing appropriate tools, your organization can disrupt the ROI of SMS toll fraud. Making it prohibitively expensive and challenging for attackers compels them to abandon their efforts, minimizing the potential impact on your business.
Global Financial Impacts
It would be difficult to understate the impact of cybercrime and SMS fraud. By some estimates, cyberattacks worldwide cost more than $6 trillion annually, equivalent to the GDP of the third-largest global economy – and a staggering 20% of them are driven by bots.1
At Arkose Labs, every day we see first-hand how bots and automated attackers incessantly attempt to infiltrate businesses across our world-wide network; their actions are a constant reminder of the dynamism in the cybercrime economy! Consider some recent Arkose Labs network stats:
- Financial services sites saw a 352% increase in bot-driven attacks in the second half of 2022
- Bots drove 97% of the attacks on fintech companies
- 1 of every 5 login attempts is an account takeover (ATO) attack
SMS toll fraud is a significant component of this picture, costing businesses more than $10 billion annually – a tenfold increase over the past decade.2 This scam has an immediate impact on your gross margin and bottom line, and ultimately inflates the costs for your business and customers.
The Mechanics behind the Attack
SMS toll fraud is an unusual threat vector in that the key telltale is transaction abandonment immediately after the bots initiate the SMS flow. In doing so, the attackers monetize quickly with few real-life consequences. They are not involved in ATO, inventory manipulation, chat scraping, or any of the other customary attacks against businesses that require more sophistication.
Rather, the crime is simple to perpetuate and organizations can easily be caught flat-footed. And in most cases, the scammers are in far away places, making any type of law enforcement or regulatory controls extremely difficult and unlikely. It’s almost a free pass for the bad actors.
Here’s how SMS toll fraud automates high-volume, high-cost SMS flows:
- Step One: Identifying Vulnerable Targets. Attackers identify businesses with SMS touchpoints, such as registration flows or account authentication, which can be exploited for fraudulent activities.
- Step Two: Obtaining Unscrupulous Numbers. Scammers acquire phone numbers from carriers who may engage in unethical practices, providing access to high-risk or expensive SMS services.
- Step Three: Integration into the Application. The obtained numbers are integrated into the attacker’s application or system, ready to be used for fraudulent activities.
- Step Four: Initiating Fraudulent Actions. Attackers initiate SMS flows using the compromised numbers, often targeting registration processes, account takeovers, or any other interactions that trigger the delivery of SMS messages.
- Step 5: Passage through Systems. The fraudulent SMS flows traverse through the entire registration system, including SMS providers and carriers, without raising suspicion or triggering detection mechanisms.
- Step 6: Billing and Financial Impact. The carrier charges the business for the high-risk, expensive numbers used in the fraudulent SMS flows. The unsuspecting victim ends up with an inflated bill for services they did not request or authorize.
- Step 7: Profit Distribution. The attacker and colluding carrier share the profits obtained from the fraudulent charges, with the carrier typically taking a significant portion of the amount…and then, rinse and repeat!
This threat vector is tailor-made for volumetric attacks. With the help of colluding carriers providing “expensive” numbers and bots to exploit those numbers en masse, you have the perfect scenario for attackers. It’s a scam that when done at scale – imagine multiple occurrences across an entire period of time – yields millions and millions of dollars in fraud losses every single month.
And the best part for the criminals? These attacks tend to go undetected for months!
Best Practices for Stopping SMS Toll Fraud
Part of the challenge of stopping SMS toll fraud is that the attacks are easy to miss while they’re underway. Oftentimes the budget owner – for example, the head of a marketing campaign to sign up new customers – isn’t the same as the person paying the bills, so there’s no direct feedback loop. By the time your organization realizes you’ve been charged for non-existent registrations, the scammer has disappeared and the money is almost impossible to recoup.
However, if you make it costly and difficult enough for cybercriminals to intrude into your business, you can stop them before they get a foot in your door. A multi-pronged approach that includes the following safeguards working in tandem can help protect your organization from attack.
Tactic #1: Baseline your good SMS spend.
What is your typical monthly SMS traffic and your typical monthly SMS spend? Establishing a benchmark of your normal traffic and expenditure for legitimate SMS usage will serve as a reference point for detecting anomalies and unusual patterns of SMS spend. Make sure to measure and adjust that baseline frequently as you roll out new registration campaigns so that your data is not stale.
Tactic #2: Measure for anomalies.
Measure early, measure often. My recommendation would be to measure for anomalies on a daily basis rather than quarterly or monthly, which would enable timely detection and response to any unusual patterns or suspicious activities in SMS usage. If you’re starting a new campaign, pay close attention to how you expect the usage to grow.
Tactic #3: Monitor and alert your one-time passcode rates.
Conversion rates can be a strong indicator of suspicious activity. Unusually high or remarkably low conversion rates may suggest that OTPs are being intercepted or manipulated, highlighting the presence of fraudulent attempts or vulnerabilities in the authentication process.
Tactic #4: Set rate limits.
Consider implementing rate limits to control your SMS spending, similar to setting a budget for Google search words or other advertising expenses. By defining a predetermined spending threshold, you can automatically throttle the spend when it reaches the limit. This practice establishes a forcing function to review the actual spend and assess your return on investment.
Tactic #5: Protect your apps against bots.
SMS toll fraud attacks come fast, and there’s a built-in velocity that can tell you immediately when you’re dealing with an attacker and not a legitimate customer. The fastest and best way to stop large volumetric attacks is with advanced bot-detection technology designed to swiftly identify and block fraudulent bot-driven activities.
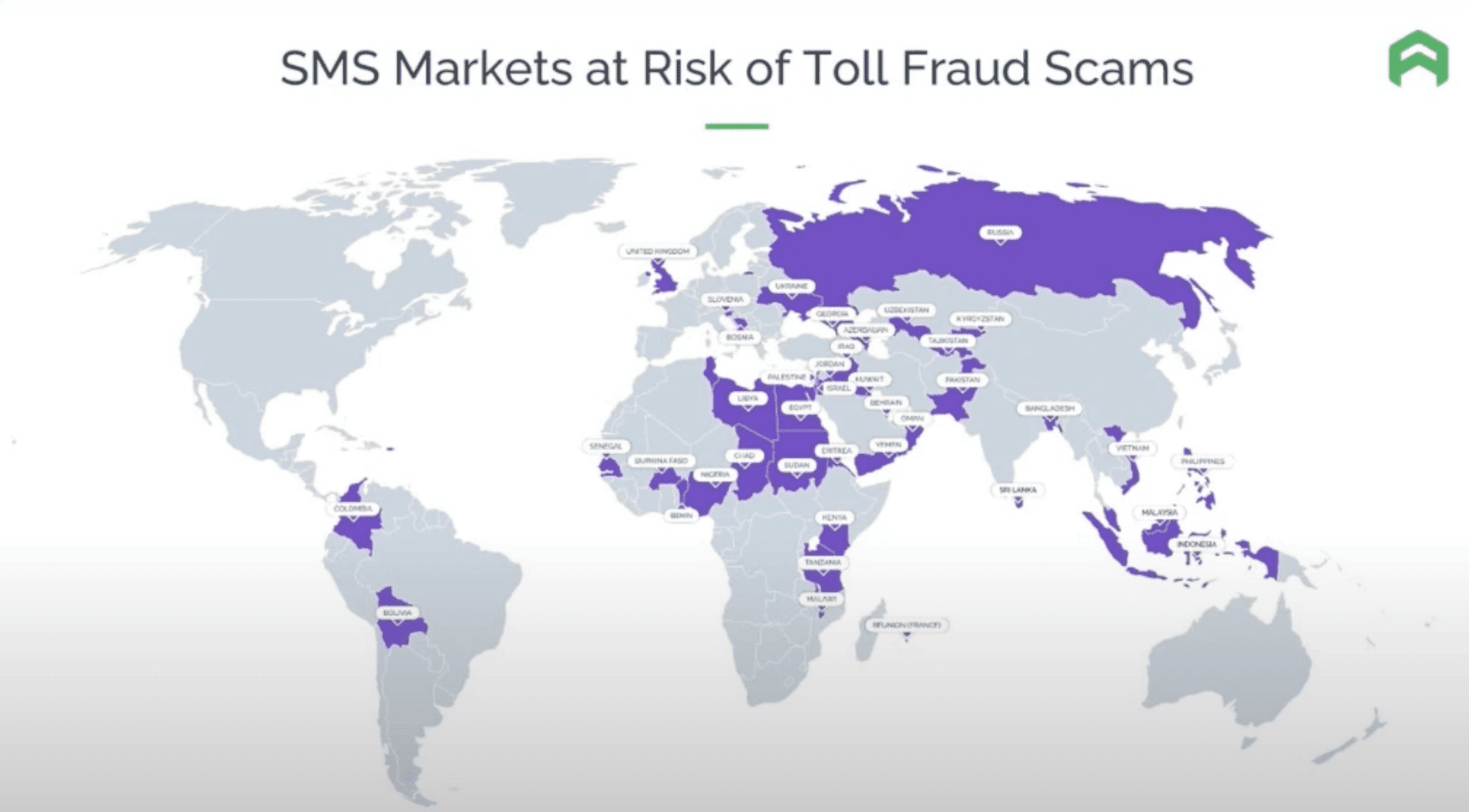
Tactic #6: Consider thoughtful geographic restrictions.
Imagine you’re in the business of selling pet food in the United States, and you’re suddenly overwhelmed with an influx of signups from Indonesia. This may be a good indication that your “customers” aren’t legitimate consumers, and you may want to consider geofencing.
How Arkose Labs Can Help
At Arkose Labs, we are in the fight! We drive attackers away by making it so expensive that the cybercriminals give up. Our bot detection and mitigation platform, Arkose Bot Manager, stops bot attacks by driving up adversarial effort and cost. With this ML-driven platform, we offer a comprehensive solution that integrates multi-layered detection mechanisms and adaptive response strategies.
By effectively interpreting ambiguous trust signals, our system ensures robust protection against attacks while maintaining a seamless user experience. Empowering security teams around the world, Arkose Bot Manager provides advanced detection capabilities, valuable risk insights, and user-friendly enforcement options to shift from mere mitigation to proactive deterrence. And, we backstop our offering with an industry-leading SMS toll fraud warranty!
Wondering how much your business can save while you break the ROI of the SMS toll fraud attacker? Explore our SMS toll fraud calculator or learn more in our on-demand webinar, SMS Toll Fraud Masterclass.
*** This is a Security Bloggers Network syndicated blog from Arkose Labs authored by Frank Teruel. Read the original post at: https://www.arkoselabs.com/blog/break-roi-sms-toll-fraud/

