The community team at Sonatype has been working hard on upgrading docker-nancy from a Post Panamax cargo ship to a new and improved Triple E vessel. (See the diagram below). As a result, the docker-nancy project on github that we announced earlier is being archived. Now, docker-nancy has moved to the main repository.
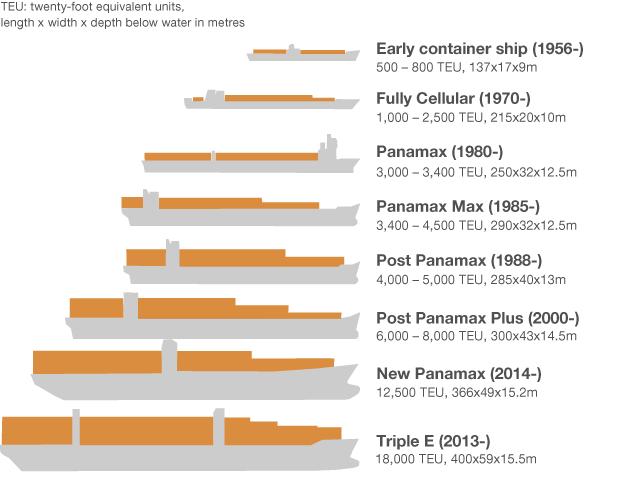
The Triple E is the largest container ship to-date. (Image Source)
Who is Nancy?
Nancy is a tool to check for vulnerabilities in your Golang dependencies, powered by Sonatype OSS Index. docker-nancy wraps the nancy executable in a Docker image.
Nancy checks for vulnerabilities in your Golang dependencies, powered by Sonatype OSS Index and Nexus IQ Server. This gives you a smooth sailing experience as a Golang developer, using the best tools in the market!
Nancy currently works for projects that use dep or go mod for dependencies.
To see how Nancy will output when finding vulnerabilities, use our intentionally vulnerable repo. Check out this build on Travis-CI or this build on CircleCI.
Bon Voyage, docker-nancy!
Ahoy! oysteR
Also new to the community is the ability to create purls from the filtered sands of your dependencies, powered by Sonatype OSS Index.
If this project is run independently, one can run:
Rscript R/main.R
main.R has a call to audit_deps_with_oss_index() by default, as a convenience.
If installed, you can do:
library(oysteR)
oysteR::audit_deps_with_oss_index()
This will accomplish the same behavior as running main.R.
Reminder: Neither Are Officially Supported by Sonatype (And More Contributions Are Available)
It is worth noting that oysteR and Nancy are NOT SUPPORTED by Sonatype. Both are contributions to the open source community (read: you!).
Remember:
- Use these contribution at the risk tolerance that you have
- Do NOT file Sonatype support tickets (Read more...)