4 Ways to Guard Against an ATM Cash-out
Breach-proof Your Bank’s ATMs
In a spine-chilling warning issued recently, the  Federal Bureau of Investigation (FBI) has cautioned banks across the globe of an inevitable, worldwide cyber attack known as ‘ATM Cash-out’.
Federal Bureau of Investigation (FBI) has cautioned banks across the globe of an inevitable, worldwide cyber attack known as ‘ATM Cash-out’.
‘ATM Cash-out’ is a meticulously planned, highly choreographed, global cyber attack wherein hackers breach a bank or payment card processor’s cybersecurity systems and use cloned debit cards at multiple ATM machines around the world to fraudulently withdraw millions of dollars within a short period of time.
For Indian banks, the FBI’s warning comes at an ominous time when the banking fraternity was slowly coping up from the recent ATM Cash-out cyber attack on the Pune-headquartered Cosmos Bank in which the hackers siphoned off Rs. 94 crores in 2 days.
What exactly happened at Cosmos Bank?
The cyberattack at Cosmos Bank, one of India’s oldest urban cooperative banks, resulted in two fraudulent transactions:
ATM Cash-out: On 11th August, hackers cloned the Visa and Rupay debit cards of the bank’s users and siphoned off Rs. 80.5 crores through 15,000 ATM cash withdrawal transactions across 28 countries within 2 days.
SWIFT Fraud: On 13th August, the hackers transferred around Rs. 14 crores to a Hong Kong-based bank using SWIFT – the globally accepted messaging system used by most banks to facilitate cross-border monetary transactions.
To enable both of these fraudulent transactions, the hackers infiltrated the bank’s systems, stealthily inserted a malware and created a Proxy Switch for the bank’s payment gateway partners Visa and Rupay. This Proxy Switch was then used to bypass the bank’s Core Banking System (CBS) and authorise the fraudulent transactions to siphon off money.
How Gemalto helps Banks breach-proof their ATM ecosystem
As the global leaders in Digital Security, Gemalto has been helping banks across the globe safeguard their ATM ecosystem for decades.
Gemalto’s robust, policy-driven solutions protect data from source to destinations using state-of-the-art technology to secure confidential data throughout its lifecycle and through the multiple layers of its traversal.
These solutions provide a comprehensive 3-tier security that revolves around 3 core principles: encrypting and tokenizing the data, digitally signing all sensitive transactions and, securely storing and managing the cryptographic keys centrally.
Below are 4 ways in which banks can safeguard their ATM ecosystem:
- Point-to-Point Data Encryption and Tokenization
Gemalto’s SafeNet Data Encryption solutions seamlessly encrypt all sensitive data – both at the backend as well as the one available on the debit cards, thereby rendering the data useless to attackers.
To mask sensitive information, Gemalto’s Tokenization Manager automatically generates a random surrogate value (also known as a Token or Reference Key) for each Bank Account and Debit Card Number. It is this Token that is shared with all internal applications while the encrypted data is stored securely at the backend.
How it works:
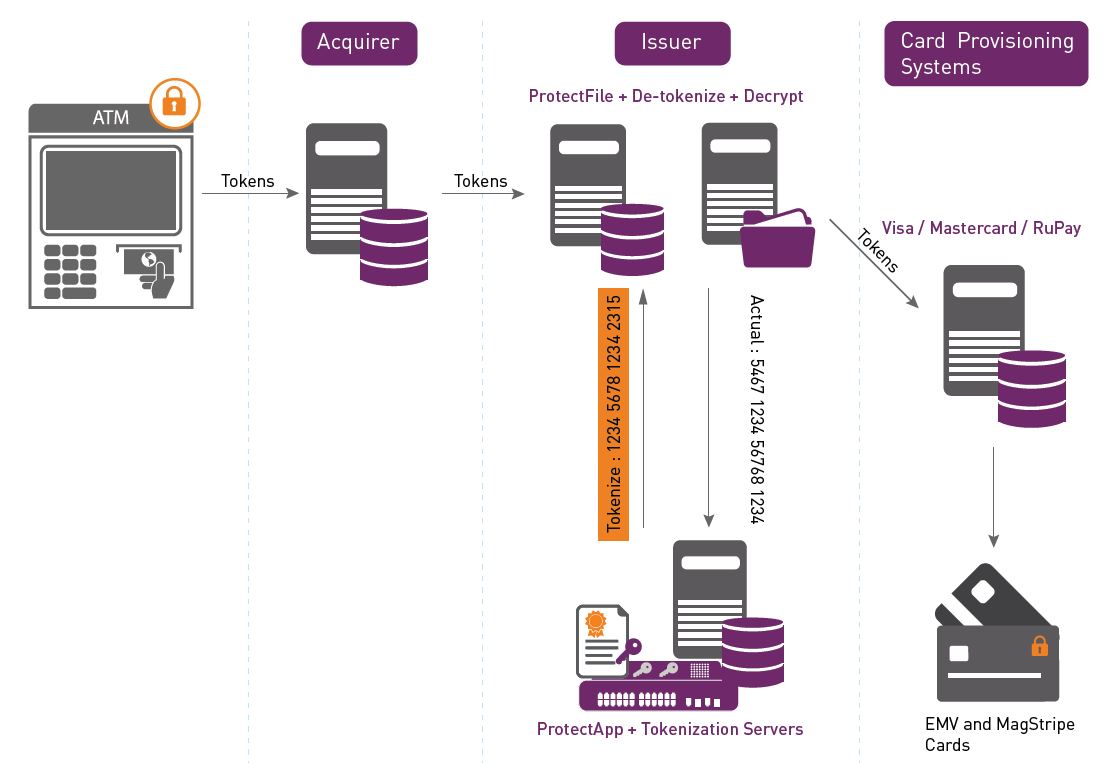
If banks encrypt and tokenize their sensitive data (like Bank Account Number, Debit Card Number, etc.), cloning would be almost impossible without the corresponding decryption keys.
- Digital Transaction Signing
Digital signing of all sensitive transactions adds an additional layer of security to prevent unauthorised access by digitally signing and verifying all transactions with a key pair approach.
Simply put, when a transaction is initiated, a ‘Private Key’ is generated which is used to sign the transaction data and a corresponding ‘Public Key’ is used to authenticate the transaction.
Illustration:
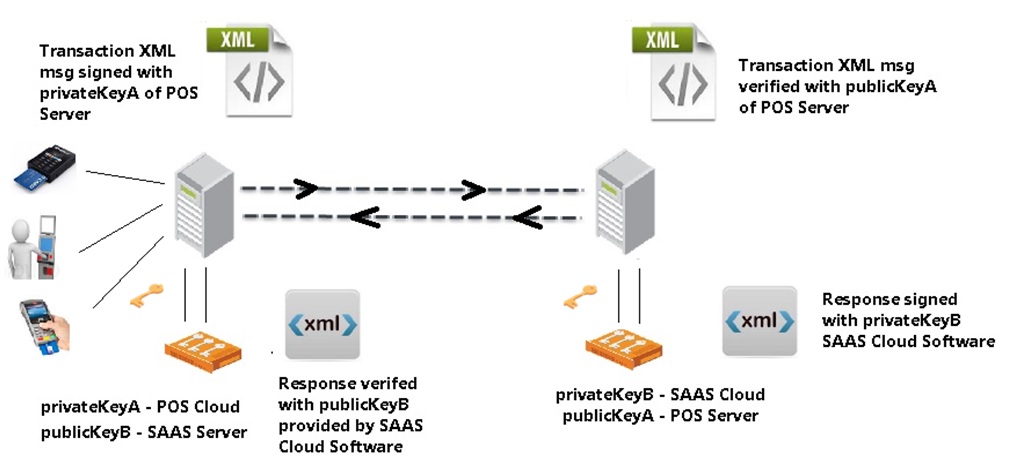
If banks adopt a PKI-based Digital Signatures approach for all their sensitive transactions, any malicious program would need access to the securely stored PKI credentials to even initiate the transaction.
Similarly, if only digitally signed applications using code-signing techniques were allowed to operate, planting the malware would have been almost impossible.
The moment the hackers attempted to plant the malware, the bank’s ATM Switch would have verified the malware’s digital signature with the one authorised by the bank, and instantly raised an incident alert upon detecting the malware was an unauthorised software.
Further, within the respective ATMs, the digitally signed request would authenticate the command sent to the Cash Dispenser from the ATM Controller and declined the cash withdrawal request upon detecting that command was issued by an interloper using a Proxy Switch.
Digital Signing is a virtual guarantee that every application or software has been authorised before executing any transaction request.
- Multi-Factor Authentication
To prevent processing of unauthorised transactions, applications and end-points that process monetary transactions, e.g. POS terminals, should add an additional factor of authentication like a One-time Password (OTP) with a pre-defined expiry time.
While ATMs and Switching solutions seldom incorporate these additional safety measures today, it is high time banks seriously consider implementing these measures considering the high probability of frequent cyber attacks on ATMs. It may also be a prudent move to consider these additional measures for applications like SWIFT that process high-value transactions.
- Secure Key Storage and Management
Protecting the encryption keys of sensitive information (such as Bank Account Numbers) and Digital Signatures (for transactions) from any compromise requires a robust safety mechanism.
If the cryptographic keys are compromised in any way, the entire cybersecurity ecosystem of banks can be affected. To ensure optimal security, banks need to use the state-of-the-art Hardware Security Modules (HSMs) to protect their Private Keys used for encrypting data.
HSMs are dedicated crypto processors that are specifically designed for storing and protecting the cryptographic (encryption) keys inside a hardened, tamper-resistant hardware device.
While traditional HSMs suffice in securely storing the cryptographic keys, they severely lack in a critical aspect – Key Management. Since crypto keys pass through multiple phases during their lifecycle – like generation, storage, distribution, backup, rotation, and destruction, efficiently managing these keys at each stage plays a pivotal role in optimal data protection.
Gemalto’s SafeNet HSMs come with a built-in Key Management feature that provides a single, robust, centralized platform that seamlessly manages the crypto keys at each stage.
Further, SafeNet HSMs provide the highest level of security, as the encryption keys never leave the intrusion-resistant, tamper-evident, FIPS-validated device. Since all cryptographic operations occur within the SafeNet HSM device, strong access controls (through IP Whitelisting) cohesively verifies user identity and prevents unauthorised commands from untrusted applications.
Learn how Gemalto can cohesively help banks mitigate their ATM risk, download our Mitigate Banking Customer ATM Risk FREE Whitepaper or visit our Financial Data Security page for more information.
Summary
When it comes to safeguarding your bank’s cybersecurity, ignorance is not a bliss! With cyber attacks getting more sophisticated and frequent, there is no room for vulnerability – the risks are all too real, as seen in the case of the Cosmos Bank breach.
In the ever-evolving cosmos of cyber attacks, prevent your bank from becoming the next victim. Upgrade your bank’s ATM cybersecurity apparatus now before it is too late.
*** This is a Security Bloggers Network syndicated blog from Enterprise Security – Gemalto blog authored by Prasun Srivastava. Read the original post at: https://blog.gemalto.com/security/2018/09/11/4-ways-guard-against-atm-cash-out/

